This blog walks cybersecurity professionals through the logical steps to create a practical and actionable cybersecurity strategy.
Your cybersecurity strategy must clearly articulate how you will address your Risk Statements and realize your Future State and Vision.
This is where the rubber hits the road. What, specifically are you seeking to accomplish with your strategy and what tasks must be accomplished to get there? This stage will provide the logical outline of tasks, initiatives and projects that will eventually go into you Roadmap (more on that in Step Nine).
At this point, you must state your Objectives and the Key Results (OKRs) associated with operationalizing your strategy. You first have to define your Objectives and, once you have done that, then the Key Results required to accomplish each[1].
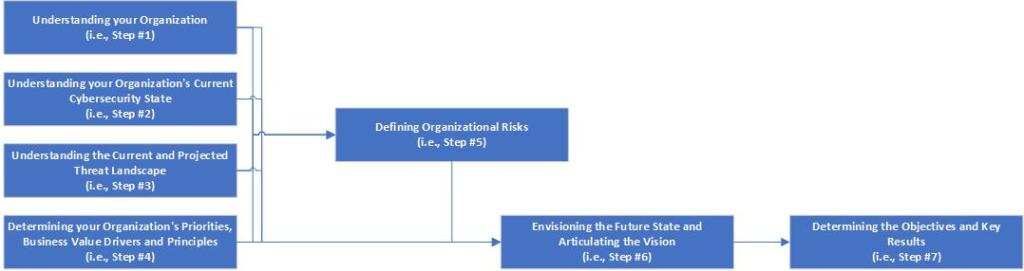
But how do you articulate the objectives? You should have everything you need from the prior steps. Consider the following diagram:
To get here, you have:
- Worked to understand the organization’s Purpose, Priorities, its current Cybersecurity Capabilities, and the Threats it is likely to face (i.e., Steps 1-4).
- Used that information to define the Risks to the Organization (i.e., Steps 5).
- Used all of the information and analysis from the prior five steps to envision a Future State and accordingly define a Vision Statement (i.e., Step 6).
So now:
- Your Objective(s) should logically flow from the prior steps to determine on what major areas you will need to focus.
I won’t get into what the objectives should be as there will be too much variability. But I will say this:
The objective should frame an accomplishment that can be directly attributed to a critical element of the future state.
Side Note:
If, for example, the envisioned Future State depends in great part on the modernization of the organization’s Identity and Access Management (IAM) framework, and the current scope of IAM is limited or has coverage gaps, one possible Objective statement could be: Identity governance is established across all human and non-human digital identities across all hosting models.
Once you have defined your Objectives, you can then consider what specific series of tasks must be delivered in order to accomplish them (i.e., the Key Results).
When working to define your OKRs, here are a few things to consider.
The Objectives Must Connect Back to Risks, Business Priorities and Future State
The whole point of this exercise is so that you can – with facts and evidence – demonstrate to the organization’s key decision makers that the Objectives of the strategy are solidly grounded in the organization’s own priorities, goals and objectives. Having followed the steps outlined in the graphic above, you can easily provide the background data that supports how your objectives will directly address the business’s needs. By doing so, you are also by the way, demonstrating how the envisioned Future State is also addressing those needs.
Side Note:
In order to ensure the operationalization of the Strategy is feasible, it is recommended to try to restrict the number of Objectives to no more than five. Creating more may make the realization of the strategy unrealistic, prohibitively expensive and/or complex. If you feel this is too small a number, use your best judgement. In this case, prioritize the Objectives and, for those un-realized Objectives, create a Risk Register (i.e., as mentioned in “Cybersecurity Strategy Step Two: Where Are You?”)
Key Results Must Together Achieve the Objective
The Key Results for an Objective should be thought of those activities that, when delivered, will accomplish the stated Objective. They should together comprise the sum total of all activities that will be required.
Depending on their complexity, the Key results can be framed in the form of tasks, initiatives, projects, or full programs. Many of these may already have been developed in some form or other during the establishment of the organization’s current Cybersecurity State (i.e., “Cybersecurity Strategy Step Two: Where Are You?”).
The Key Result should be framed as a tactical activity that can achieve a specific goal. For example, you could draft the folowing Key Result:
“Modernize Privileged Access: Leverage Security technologies to modernize and enforce Privileged Access policies and procedures.”
You must keep it specific however and not try to generalize across multiple areas of focus (e.g., keeping Threat Detection separate from Incident Response).
Side Note:
To help ensure the execution and delivery of the Key Results, it is recommended to try to restrict the number derived to no more than five per Objective. As above with Objectives, too many Key Results may make the delivery unwieldly and overly complicated. Remember however, that some Key Results – if complex enough – may be defined in terms of a long-term program of sub-projects. This assumes a lengthy delivery and the involvement of a number of dedicated resources focused on this one area. In those cases, phrase the Key Result to encompass all that the program would deliver.
Key Results Must Be Measurable
One crucial element of the Key Results, however, is that their delivery must be measurable in some way. This is already true of most projects and programs, so should come as little surprise[2]. The Key Result must have some measurement to indicate whether it was successful in it’s aim (e.g., “100% of privileged human identities are identified and under full governance.”, “Migrate all 3rd-party developers to a secure virtual desktop environment within 6 months.”, “Enrol at least 80% of laptops in MDM by the end of the calendar year.”, etc.). The scope is very important here.
Side Note:
Determining measurements for your Key Results may be premature at this stage. It requires a great deal of collaborative discussion and agreement on what success looks like. At this stage, focus your efforts on defining the Objectives and the Key Results that will accomplish them. Defining the scope and measurement of success for a Key Result may best be done during the creation and drafting of the Cybersecurity Strategy’s Operational Roadmap (i.e., “Cybersecurity Strategy Step Nine: How Do We Get There?”)
Finally, Key Results measurements should not necessarily be set in stone. Like most projects and programs, it is a good practice to regularly review the measurements to make sure they still make sense and whether they need to change or evolve as they work progresses.
Thank you for your time. Be sure to stay tuned for the next posting in this series: Cybersecurity Strategy Step Eight – How Do We Know When It’s Working? (Defining Metrics).
[1] In Agile terminology, you can think of the Objectives as Epics and the Key Results as the Features (i.e., components that contribute to the Epic).
[2] In Agile terminology, you can think of the Measurable aspects of the Key Results as the User Story (i.e., user value story that contributes to the Feature).
Leave a comment